Introduction#
Traditional security architectures rely heavily on a secure network perimeter — often referred to as the “castle and moat” model. In this approach, users and devices inside the corporate network are considered trusted, while those outside are treated as threats. However, as workforces become more distributed and applications move to the cloud, this perimeter-based security model has become increasingly outdated and vulnerable.
To address this shift, Google introduced BeyondCorp, a security model that replaces the traditional notion of network trust with context-aware access. It is Google’s implementation of the Zero Trust model, where trust is not granted based on network location but is instead determined dynamically based on a user’s identity, device state, and other contextual signals.

What Is BeyondCorp?#
BeyondCorp is an enterprise security architecture that enables secure access to internal applications without using a traditional VPN. It treats both internal and external networks as untrusted and shifts access controls from the network layer to the application layer.
Access decisions are based on multiple factors, including:
- The identity of the user
- The device being used
- The security posture of that device (such as patch level or antivirus status)
- Real-time context, such as location or time of day
The core philosophy of BeyondCorp is: trust nothing, verify everything.
Why BeyondCorp Matters#
The shift to cloud-native applications, increased use of personal devices, and the rise of remote work have all contributed to the need for a more modern approach to enterprise security. BeyondCorp offers several key advantages:
- Improved security posture: Reduces reliance on perimeter-based defenses that can be bypassed.
- User flexibility: Allows users to work securely from any location, on any device.
- Granular access control: Provides fine-grained policy enforcement based on real-time context.
- Reduced attack surface: Internal apps no longer need to be exposed on a private network or VPN.
Core Components of BeyondCorp#
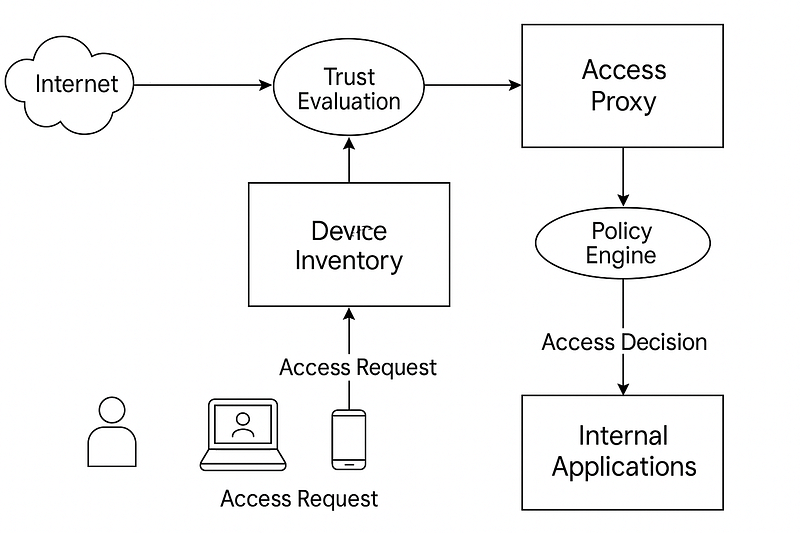
While Google’s internal implementation of BeyondCorp is complex and highly customized, its core architecture revolves around several fundamental components:
- Access Proxy: Acts as a gatekeeper to applications, enforcing policy decisions.
- Trust Evaluation: A system that continuously assesses the trust level of users and devices.
- Policy Engine: Evaluates context and enforces access rules based on defined policies.
- Device Inventory: Maintains a real-time catalog of known devices and their security state.
- Identity Provider: Authenticates users and supports federation with other identity services.
How It Works in Practice#
When a user attempts to access an internal application, the request is intercepted by the Access Proxy. This proxy gathers information about the user’s identity, the device being used, and any other relevant context. It then sends this information to the Policy Engine.
The Policy Engine evaluates the request against configured access policies. For example, access may be granted only if the device is managed, encrypted, and running the latest OS version. If the request complies with the policy, access is granted. If not, the request is denied or redirected for remediation.
This evaluation happens every time a user tries to access a resource, ensuring continuous verification rather than one-time authentication.
Implementing BeyondCorp Principles with Google Cloud#
Google Cloud provides services that help organizations adopt BeyondCorp principles, even if not implementing the full architecture from scratch. Key tools include:
- Identity-Aware Proxy (IAP): Controls access to applications hosted on GCP based on user and device identity.
- Context-Aware Access: Enables administrators to define and enforce access policies based on context like location, device security status, or group membership.
- Cloud Identity and Access Management (IAM): Grants access to resources based on roles assigned to verified identities.
Using these tools, organizations can begin adopting Zero Trust practices without overhauling their entire infrastructure.
Challenges and Considerations#
Adopting BeyondCorp requires a mindset shift and careful planning. Challenges include:
- Device management: Ensuring visibility and control over all devices accessing enterprise resources.
- Policy complexity: Creating fine-grained access rules can be difficult to scale without automation.
- User experience: Striking a balance between strong security and seamless access is crucial.
- Integration: Existing infrastructure may need to be modified to work with BeyondCorp-style proxies and access control systems.
Despite these challenges, incremental adoption — starting with high-risk apps or remote workflows — can deliver immediate benefits.
Best Practices#
- Start with identity and device inventory — ensure every user and device is known and managed.
- Implement least privilege access with tightly scoped IAM roles.
- Use continuous evaluation instead of relying on one-time logins.
- Prioritize applications with high sensitivity for initial rollout.
- Monitor and log all access requests for ongoing auditing and policy tuning.
Conclusion#
BeyondCorp represents a fundamental rethinking of enterprise security, aligning better with the realities of modern work environments. By eliminating the assumption that network location implies trust, it creates a more resilient and adaptable security model.
Organizations moving toward BeyondCorp principles can improve security, support flexible work models, and gain better visibility into user and device behavior. While full implementation may be complex, tools like Identity-Aware Proxy and Context-Aware Access make it easier to get started within the Google Cloud ecosystem.
By Safwan Luban on April 7, 2025 4:24 AM (UTC). Canonical link Exported from Medium on February 17, 2026.
Reply by Email